Vigor 2820
 ADSL2/2+ a Ethernet router poskytuje dvě vzájemně nezávislé WAN rozhraní s možnosti řízení průtoku a vzájemné náhrady. Zařízení podporuje také množství dalších funkcí nutných pro zvýšení bezpečnosti, vzdálený přístup, multimediální podporu a vytváření virtuálních privátních sítí (VPN) přes internet v jednom kompaktním zařízení, včetně možnosti připojení sdílené tiskárny, přes tiskový USB port.
ADSL2/2+ a Ethernet router poskytuje dvě vzájemně nezávislé WAN rozhraní s možnosti řízení průtoku a vzájemné náhrady. Zařízení podporuje také množství dalších funkcí nutných pro zvýšení bezpečnosti, vzdálený přístup, multimediální podporu a vytváření virtuálních privátních sítí (VPN) přes internet v jednom kompaktním zařízení, včetně možnosti připojení sdílené tiskárny, přes tiskový USB port.
Dual WAN router ADSL2+
|
 |
Router splňuje v plném rozsahu směrnice Evropského parlamentu a rady 2002/95/EC tzv. RoHS platné od 1.6.2006
Zajímavé odkazy:
1. Dual-WAN
- Outbound Policy-based Load-balance
- BoD ( Bandwidth On Demand )
- WAN Connection Fail-over
2. ADSL Compliant ( DSL )
- ANSI T1.413 Issue2
- ITU-T G.992.1 G.dmt
- ITU-T G.992.2 G.lite
- ITU-T G.992.3 ADSL2 G.dmt.bis
- ITU-T G.992.5 ADSL2+
- Multi-PVC
- Annex L ( READSL )
- Annex M *
3. ATM Protocols ( DSL )
- RFC-2684 / RFC-1483 Multiple Protocol over AAL5
- RFC-2516 PPP over Ethernet
- RFC-2364 PPP over AAL5
- PPPoE Pass Through LAN / WLAN
- PPPoE / PPPoA Relay
- Transparent Bridge for MPoA
4. VPN
- Až 32 VPN tunelů
- Protokoly:
- PPTP
- IPSec
- L2TP
- L2TP over IPSec
- Šifrování:
- PPTP
- MPPE
- Hardware-based AES
- DES
- 3DES
- Autentifikace:
- Hardware-based MD5
- SHA-1
- IKE autentifikace:
- Pre-shared Key
- Digital Signature ( X.509 )
- LAN-to-LAN , Teleworker-to-LAN
- NAT-Traversal ( NAT-T )
- Dead Peer Detection ( DPD )
- VPN Pass-through
5. Firewall
- Policy-based Firewall
- CSM ( Content Security Management ) for IM / P2P Application and URL / Web Content Filter
- Multi-NAT / DMZ Host / Port-Redirection / Open Port
- SPI ( Stateful Packet Inspection ) ( Flow Track )
- DoS / DDoS Prevention
- IP address Anti-spoofing
- Upozornění na E-Mail a zápis do Syslogu
- Vazba IP a MAC
6. Bandwidth Management
- QoS :
- Garance šířky pásma pro VoIP
- Class-based Bandwidth Guarantee by User-Defined Traffic Categories
- DiffServ Code Point Classifying
- 4-úrovňová priorita pro každý směr ( příchozí / odchozí )
- Bandwidth Borrowed
- Bandwidth / Session limitation
7. WAN Protocol ( WAN2 )
- DHCP klient
- Statická IP
- PPPoE
- PPTP
- BPA
- L2TP*
8. Network Feature
- Port-based VLAN
- DNS Cache / Proxy
- DHCP klient / Relay / Server
- IGMP Proxy
- DynamickéDNS
- NTP klient
- Plánování hovorů
- RADIUS Client
- UPnP
- Routovací protokol :
- Static Routing
- RIP V2
9. USB
- 3G USB Modem ( 3G může být aktivní pouze jako WAN2 )
- Tiskárna USB
10. Správa sítě
- Web-based User Interface ( HTTP / HTTPS )
- Rychlý průvodce startem
- CLI ( Command Line Interface , Telnet / SSH )
- Administrace kontroly přístupu
- Configuration Backup / Restore
- Vestavěné diagnostické funkce
- Aktualizace firmwaru přes TFTP / FTP / HTTP / TR-069
- Zápis do Syslogu
- SNMP Management MIB-II
- TR-069
| Hardware Interface | ADSL | 1-port ADSL2+, RJ-11 connector (for AnnexA) | |
| 1-port ADSL2+, RJ-45 connector (for AnnexB) | |||
| LAN | 3-port 10/100 Base-Tx and 1 port 1000 Base-TX Switch, RJ-45 connectors | ||
| WAN | 1 port 10/100 Base-Tx, RJ-45 connector | ||
| USB | 1-port USB Host 2.0 (USB Printer / 3G USB Modem) | ||
| Dual WAN | Outbound Policy-based Load-balance | ||
| Bandwidth On Demand | |||
| WAN Connection Fail-over | |||
| ADSL Compatibility | ANSI T1.413 Issue2 | ||
| ITU-T G.992.1 G.dmt | |||
| ITU-T G.992.2 G.lite | |||
| ITU-T G.992.3 ADSL2 G.dmt.bis | |||
| ITU-T G.992.5 ADSL2+ | |||
| Annex L (READSL) | |||
| Annex M * | |||
| ATM Protocol | RFC-2684 / RFC-1483 Multiple Protocol over AAL5 | ||
| RFC-2516 PPP over Ethernet | |||
| RFC-2364 PPP over AAL5 | |||
| PPPoE Pass Through LAN | |||
| PPPoE / PPPoA Relay | |||
| Transparent Bridge for MPoA | |||
| VPN | Up to 32 VPN Tunnels | ||
| Protocol : PPTP, IPSec, L2TP, L2TP over IPSec | |||
| Encryption : MPPE and Hardware-based AES / DES / 3DES | |||
| Authentication : Hardware-based MD5, SHA-1 | |||
| IKE Authentication : Pare-shared Key and Digital Signature (X.509) | |||
| LAN-to-LAN, Teleworker-to-LAN | |||
| DHCP over IPSec | |||
| NAT-Traversal | |||
| Dead Peer Detection | |||
| VPN Pass-through | |||
| Firewall | Policy-based Firewall | ||
| Content Security Management for IM / P2P Application and URL / Web Content Filter | |||
| Multi-NAT / DMZ Host / Port-redirection / Open Port | |||
| Stateful Packet Inspection (Flow Track) | |||
| DoS / DDoS Prevention | |||
| IP address Anti-spoofing | |||
| E-Mail Alert and Logging via Syslog | |||
| IP and MAC Binding | |||
| Bandwidth Management | QoS | Class-based Bandwidth Guarantee by User-Defined Traffic Categories | |
| DiffServ Code Point Classifying | |||
| 4-level Priority for Each Direction (Inbound / Outbound) | |||
| Bandwidth Borrowed | |||
| Bandwidth / Session Limitation | |||
| WAN Protocol (WAN2) | DHCP Client | ||
| Static IP | |||
| PPPoE | |||
| PPTP | |||
| BPA | |||
| L2TP* | |||
| Network Feature | DNS Cache / Proxy | ||
| DHCP Client / Relay / Server | |||
| IGMP Proxy | |||
| Dynamic DNS | |||
| NTP Client | |||
| Call Scheduling | |||
| RADIUS Client | |||
| UPnP | |||
| Routing Protocol | Static Routing | ||
| RIP V2 | |||
| Network Management | Web-based User Interface (HTTP / HTTPS) | ||
| Quick Start Wizard | |||
| CLI (Command Line Interface , Telnet / SSH) | |||
| Administration Access Control | |||
| Configuration Backup / Restore | |||
| Built-in Diagnostic Function | |||
| Firmware Upgrade via TFTP / FTP / HTTP / TR-069 | |||
| Logging via Syslog | |||
| SNMP Management MIB-II | |||
| TR-069 | |||
| TR-104* | |||
| Support Smart Monitor | Up to 30 PCs | ||
|
Temperature
|
Operating : 0°C ~ 45°C | ||
| Storage : -25°C ~ 70°C | |||
| Humidity | 10% ~ 90% (non-condensing) | ||
| Max. Power | 10 Watt | ||
| Dimension | L241 * W165 * H44 (mm) | ||
| Power | DC 12V ~ 15V | ||
...
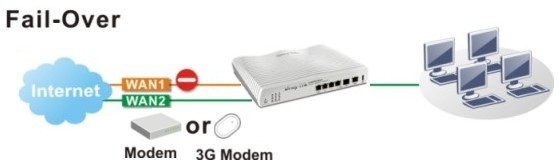
Dual WAN Load Balancing / Fail Over |
||

|
||
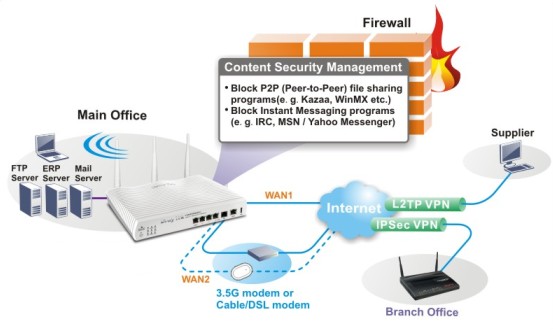
VPN Firewall Application |
||
| With hardware-based implementation of the VPN protocol, the Vigor2820 supports up to 32 VPN tunnels using advanced protocols such as IPSec / PPTP / L2TP / L2TP over IPSec with AES / DES / 3DES for encryption and MD5 / SHA-1 for authentication.
The SPI firewall uses Object-Based design to make setting of firewall policies easy. The CSM feature allows more precise and efficient access control for URL / Web Content Filtering, IM and P2P applications. 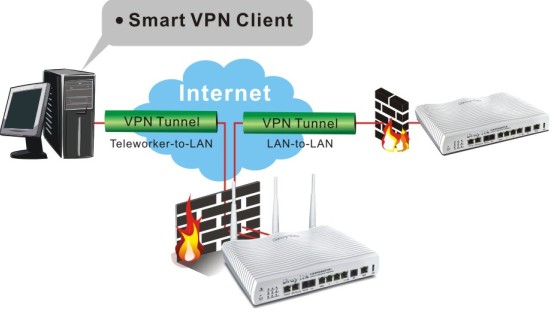
|
||
CSM / 3.5G Fail-over Backup |
||
|
Vigor2820 series' CSM (Content Security Management) function can block selected P2P and instant message applications. This would not only help employees stay focused on their job but also prevent possible treats from those applications damaging corporate essential data severs. 3.5G fail-over backup can keep business continuous during downtime of the leased line from ISP.
|
Aktuálni informace o produktech série Vigor2820
|